Cyber Crime and Punishment
Cops and robbers.
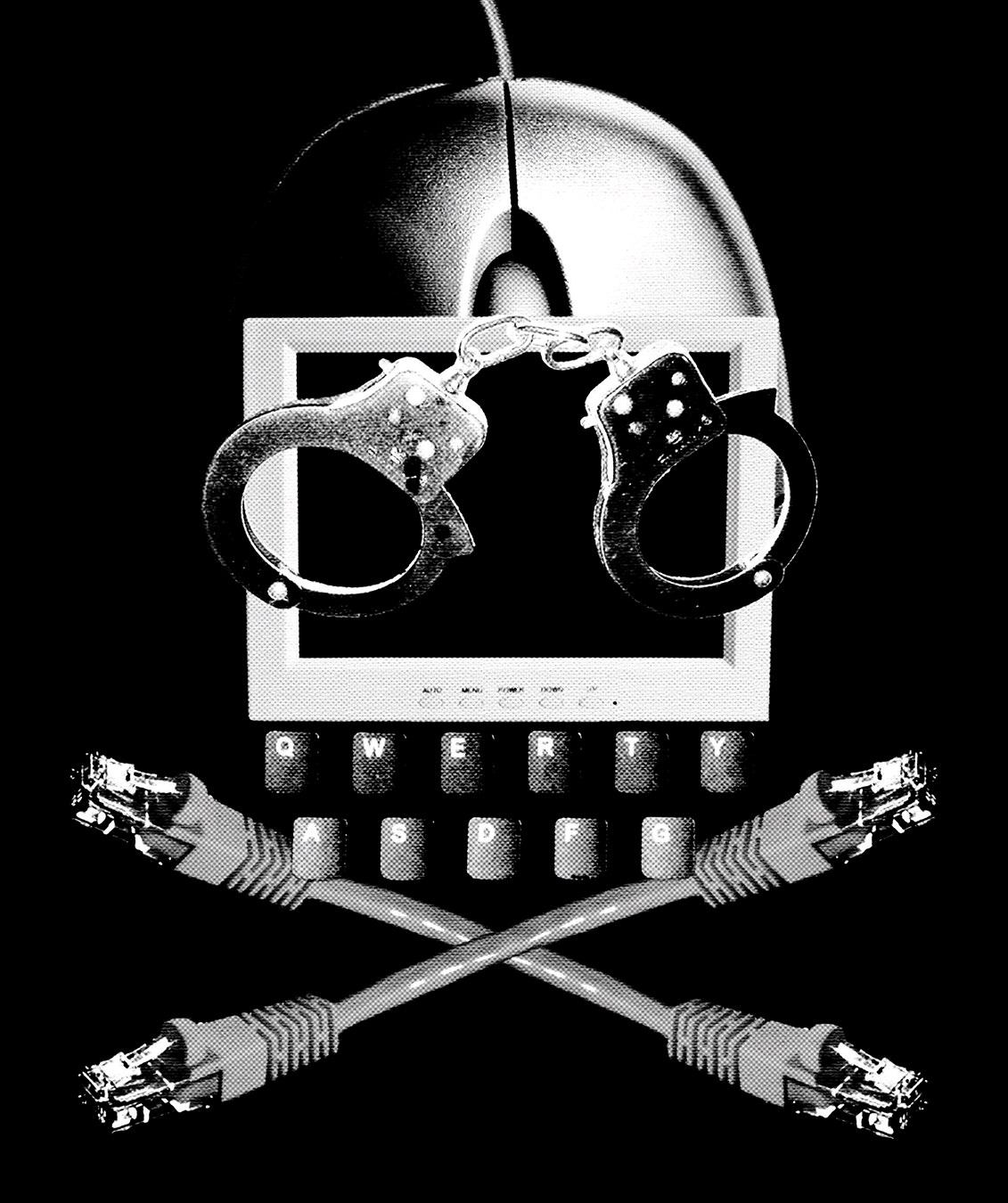
Illustration by Mark Reynolds.
Crime, we are told, does not pay. Clearly someone forgot to pass on the memo to Nigeria, where enterprising crooks have transformed an age-old confidence trick into a significant, if scandalous, contribution to the African nation’s GDP.
For nearly 30 years now, the 419 scam (so named for the statute in Nigeria’s criminal code that prohibits it) has been filling inboxes across cyberspace. Variations are plentiful, but most of the e-mails start with a polite invitation asking recipients to assist in the liberation of unclaimed cash left behind by a disgraced bureaucrat, deposed dictator, or similar character of ill repute. In exchange for a small “advance fee” (explained by the perpetrator as necessary for bribes, bank fees, and related expenses), marks are usually offered a slice of the much bigger pie.
For many, it is an offer too good to refuse. Despite regular warnings from governments and consumer agencies in North America and Europe, the 419 scam remains one of the world’s most lucrative frauds. Although exact figures are understandably difficult to verify, a research group in Holland recently estimated the Nigerian e-mail and similar advance-fee frauds took in more than $9.3-billion (U.S.) in 2009 alone.
The mechanics of 419 are often laughably crude (to say nothing of the syntax of the perpetrators); what isn’t is the scam’s use of cyberspace. Unlike most rip-offs, 419 is almost wholly contingent upon technology. While mail and facsimile transmissions cost money, e-mail allows con men to contact hundreds of thousands of would-be marks from half a world away for next to nothing. Internet cafés and disguised IP addresses give scammers a shroud of near-total anonymity, and fake sites, web links, and other tricks give the scam’s supporting details an aura of believability. Would 419 exist without the high-tech props? Certainly. Would it be as profitable? Certainly not.
Unfortunately, the 419 e-mail is just one example of the darker side of technology. From phishing scams to online fraud to denial-of-service attacks to cyber raids on Internet retailers, technology has become an integral part of the criminal enterprise. This despite the fact that the vast majority of users remain blissfully ignorant of what evil—be it worm, virus, or Trojan horse—lurks in the heart of their CPUs.
That may be about to change, as news of computer crime and other high-tech hijinx moves from the technology section to the front page. Take, for example, the geopolitical brouhaha created by the Stuxnet computer worm. Unlike a standard virus, whose programming is often simple and whose purpose is often only to replicate itself, Stuxnet is a sophisticated, complex program with a specific target: high-level industrial controls built by German manufacturer Siemens. The geographic concentration of infection (60 per cent of the earliest recorded infections were in Iran), along with the target’s probable purpose (Siemens components are known to control the cycle and speed of the centrifuges in Iran’s illicit uranium enrichment program) has leant an aura of Tom Clancy–esque international conspiracy to the story.
Of course, as crime evolves, so too does punishment. The rise in cybercrime has bred a new generation of cybersleuths, tasked with making cyberspace safer for businesses, government, and casual users alike.
On the front lines are companies such as Symantec (developers of the Norton AntiVirus software), Kaspersky Lab, and a host of others. Over the past decade, such companies have transformed malware identification and eradication into a multi-billion-dollar industry. In fact, so attractive are the economics of cybersecurity that microchip giant Intel recently agreed to a $7.7-billion takeover of well-known Internet security company McAfee.
Governments and quasi-government agencies have also thrown their muscle into the fight against cybercrime. The European Institute for Computer Anti-Virus Research (EICAR) has been conducting research and organizing cybersecurity conferences since 1991. On this side of the pond, the Internet Crime Complaint Center (IC3 for short), a joint venture of the FBI and the National White Collar Crime Center, acts as a kind of clearing house for cybercrime, helping victims register complaints and helping lawmakers hone their skills to stop cybercrooks.
Here at home, Canada has taken a sizable bite out of cybercrime. A team of researchers at the Citizen Lab at the University of Toronto’s Munk School of Global Affairs made a name for itself in March 2009 for pushing the reset button on GhostNet, a network of compromised computers that allowed hackers to control and steal files from infected machines in dozens of ministries and diplomatic missions around the world (the Lab fingered China as the most likely perpetrator). More recently, the team exposed Koobface, a Russian-made malware program that has bilked online advertisers out of more than $2-million by recording fraudulent click-throughs on social networking sites such as Facebook.
And then there are those who belong to neither camp—or perhaps both. Depending on your politics, WikiLeaks and the subculture of hackers that have come to its defense are either the world’s greatest cybercriminals or the primary defenders of the techno-faith. Mercenary hackers, free-web vigilantes, cybervandals—whatever label you assign them, there is little doubt they have captured both the imagination and the headlines of the age.
If nothing else, one thing seems decided: in the digital age, the cops will be armed not with guns, but with computer science degrees. Unfortunately, the same goes for the robbers.